WiFi Pineapple
-
The industry standard WiFi pentest platform has evolved. Equip your red team with the WiFi Pineapple® Mark VII. Newly refined. Enterprise ready.
 Ships in 1-3 day worldwide
Ships in 1-3 day worldwide
Orders are fulfilled from our California warehouse in 1-3 days. Typical shipping times:
- 🇺🇸 USA: 2-7 days
- 🇨🇦 Canada: 2-8 days
- 🇬🇧 UK: 3-5 days
- 🇪🇺 EU: 3-8 days
- 🦘 Australia: 3-10 days
 Insured against loss & damage
Insured against loss & damage
Orders under $2500 are automatically protected against loss & damage via MonkProtect™ shipping insurance with a fast and easy resolution center.
 EU Safety Information
EU Safety Information
Manufacturer: Hak5 LLC. 5473 Blair Rd, Ste 100 PMB 39371, Dallas, TX 75231. Shop@Hak5.org. https://shop.hak5.org
Responsible Person: Easy Access System Europe - Mustamäe tee 50, 10621 Tallinn, Estonia, gpsr.requests@easproject.com
Safety Information: Warning: Not suitable for children under 14 years. This is not a toy. Contains small parts that may present a choking hazard. Keep out of reach of children. Do not expose the device to water, excessive moisture, direct sunlight or extreme conditions (moisture, heat, cold, dust), as the device may malfunction or cease to work when exposed to such elements. Do not attempt to disassemble or repair the device yourself. Doing so voids the limited warranty and could harm you or the device. This device is not designed, manufactured or intended for use in hazardous environments requiring fail-safe performance in which the failure of the device could lead directly to death, personal injury, or severe physical or environmental damage. Wireless equipped devices are restricted to indoor use only when operating in the 2400 MHz – 2483.5 MHz frequency range within the EU and EFTA countries, as required by Article 10(10) of Directive 2014/53/EU. Battery equipped devices: do not dispose of batteries in household waste. Battery replacement must be carried out by a qualified technician. This USB-powered device complies with the EMC Directive (2014/30/EU) and meets the requirements of EN 55032 and EN 55035 for electromagnetic compatibility. This device is designed in accordance with USB-IF specifications for voltage limits, data integrity, and power safety to ensure reliable and compliant operation. This product has been designed and manufactured in accordance with the RoHS requirements and complies with the European Union’s Restriction of Hazardous Substances (RoHS) Directive 2011/65/EU and Directive (EU) 2015/863. This device is designed to operate reliably within an operating temperature range of 35ºC to 45ºC and a storage temperature range of -20ºC to 50ºC. It is rated for use in environments with 0% to 90% relative humidity (non-condensing). Proper environmental conditions must be maintained to ensure optimal performance and longevity. Made in China. This device is for authorized auditing and security analysis purposes only where permitted subject to local and international laws where applicable. Users are solely responsible for compliance with all laws of their locality. Hak5 LLC and affiliates claim no responsibility for unauthorized or unlawful use. This device is packaged with a limited warranty, the acceptance of which is a condition of sale. See Hak5.org for additional warranty details and limitations. Availability and performance of certain features, services and applications are device and network dependent and may not be available in all areas; additional terms, conditions and/or charges may apply. All features, functionality and other product specifications are subject to change without notice or obligation. Hak5 LLC reserves the right to make changes to the products description without notice. Hak5 LLC does not assume any liability that may occur due to the use or application of the product(s) described herein.
Refined and Enterprise Ready
Experience the most refined WiFi Pineapple. Intuitive interfaces guide you through WiFi auditing. Campaigns automate pentests with stunning reports. Interactive recon puts you in command of the airspace, and a compliment of dedicated radios provides enterprise-grade results.
New in Version 2.0
Integrated Dual-Band 2.4 + 5 GHz
- Automatic MK7AC Adapter compatibility
- All-in-one package: Mark VII+AC Tactical
Firmware 2.0 RC: Free Download
• Enhanced Recon • Auto-Capture Handshakes • Improved Deauth • Web UI Firewall • WPA-Enterprise Attacks • 50+ fixes & features!
Features
-
 Leading Rogue Access Point
Leading Rogue Access Point
Patented PineAP Suite thoroughly mimics preferred networks, enabling man-in-the-middle attacks -
 WPA and WPA Enterprise Attacks
WPA and WPA Enterprise Attacks
Capture WPA handshakes and imitate enterprise access points, capturing enterprise credentials -
 Precision Targeting Filters
Precision Targeting Filters
Stay within the scope of engagement and limit collateral damage with MAC and SSID filtering -
 Simple Web Interface
Simple Web Interface
Fast and intuitive with an emphasis on workflow and actionable intelligence – just click to attack -
 Cross-Platform
Cross-Platform
No software to install. Works in any modern web browser on Windows, Mac, Linux, Android, iOS
-
 Advanced Reconnaissance
Advanced Reconnaissance
Visualize the WiFi landscape and the relationships between access points and devices -
 Actionable Intelligence
Actionable Intelligence
Identify vulnerable devices, gather intelligence on the target and direct attacks -
 Passive Surveillance
Passive Surveillance
Monitor and collect data from all devices in the vicinity. Save and recall reports at any time -
 Automated Campaigns
Automated Campaigns
Guided campaign wizards deliver repeatable, actionable results with custom reports -
 Cloud C² Enabled
Cloud C² Enabled
Deploy with confidence. Remotely command and control the airwaves with Hak5 Cloud C²
MARK VII
PORTABLE WIFI PENTEST COMPANION
- 2.4 GHz 802.11 b/g/n (5 GHz/ac with module)
Single Core MIPS Network SoC - Three Dedicated Role-based Radios
With three high gain antennas - USB-C Power/Ethernet Port, USB 2.0 Host Port,
Single RGB LED Indicator - 256 MB RAM, 2 GB EMMC
- Power via USB-C
ENTERPRISE
FULL SPECTRUM ENTERPRISE SENTRY
- 2.4/5 GHz 802.11 a/b/g/n/ac/ac wave2
Quad Core ARM Network SoC - Four Dedicated Role-based 2:2 MIMO Radios
with eight high gain antennas - Dual Gigabit Ethernet, USB 3.0 Host Port,
USB-C Ethernet Port, Four RGB LED Indicators - 1 GB RAM, 4 GB EMMC
- Power via AC
Refinements

Configuration Warnings

Notifications

Signal Strength

Device Manufacturer

Web Shell

Keyboard Shortcuts

Dashboard Overview
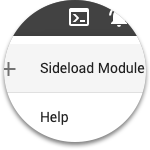
Sideload Modules

Mobile View

Client History

Time Synchronization

WiFi QR Codes

OTA Updates

Beta Channels

Cloud C2 Provisioning

Dark Theme
 See it in action. Tag #wifipineapple — Mention @hak5gear.
See it in action. Tag #wifipineapple — Mention @hak5gear.
VII Basic
VII+AC
WiFi Pineapple
✔
✔
5 GHz Adapter
✔
Decals
✔
x







 Leading Rogue Access Point
Leading Rogue Access Point WPA and WPA Enterprise Attacks
WPA and WPA Enterprise Attacks Precision Targeting Filters
Precision Targeting Filters Simple Web Interface
Simple Web Interface Cross-Platform
Cross-Platform Advanced Reconnaissance
Advanced Reconnaissance Actionable Intelligence
Actionable Intelligence Passive Surveillance
Passive Surveillance Automated Campaigns
Automated Campaigns Cloud C² Enabled
Cloud C² Enabled

